Hello Friends,
This is my second write-up on a vuln machine Toppo 1 made by my bro Hadi Mene.
Let's get Started ....
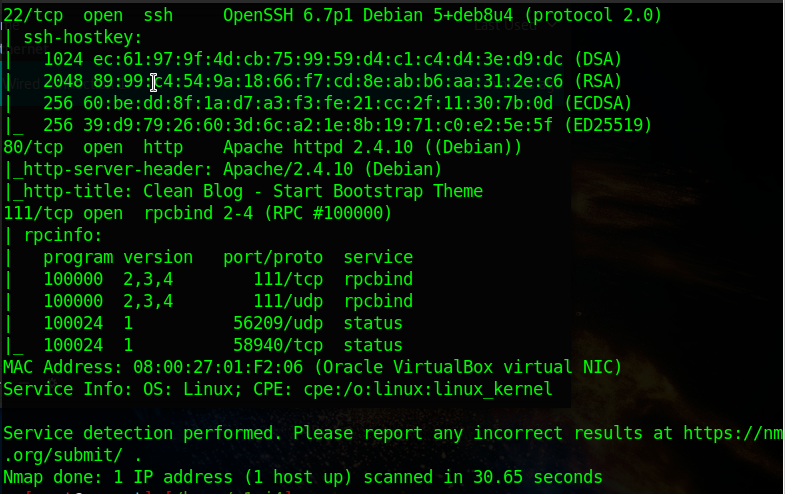
After running nmap for the target machine , I found port 80 was open so I started enumerating from there.
The first thing I try for any web app based challenge is - Running Dirbuster ;)
Found an interesting file i.e notes.txt . Let's check it out in browser .
Great, we got some password. It can be ssh credential or ftp etc. Since ftp port is closed therefore let's go for ssh login .
Tried ted123 and ted as username . Luckily "ted" worked for me .
So username - ted
pass- 1234ted123
Now comes the privilege escalation part . This was the easiest part since this covers the basics of privilege escalations through SUID.
I checked for the binaries whose setuid were enabled .
setuid bit-
That moment when you see python binary with setuid enabled.
I wrote a small python script in-order to run system commands .
Running this script with python2.7 helped me run commands with root privileges.
Yippeee !!! Easy and Good for Beginners :)
Don't forget to study more about SUID ;) Thanks for reading .. !!
This is my second write-up on a vuln machine Toppo 1 made by my bro Hadi Mene.
Let's get Started ....
After running nmap for the target machine , I found port 80 was open so I started enumerating from there.
The first thing I try for any web app based challenge is - Running Dirbuster ;)
Found an interesting file i.e notes.txt . Let's check it out in browser .
Great, we got some password. It can be ssh credential or ftp etc. Since ftp port is closed therefore let's go for ssh login .
Tried ted123 and ted as username . Luckily "ted" worked for me .
So username - ted
pass- 1234ted123
Now comes the privilege escalation part . This was the easiest part since this covers the basics of privilege escalations through SUID.
I checked for the binaries whose setuid were enabled .
setuid bit-
Binaries with the setuid bit enabled, are being executed as if they were running under the context of the root user.
That moment when you see python binary with setuid enabled.
I wrote a small python script in-order to run system commands .
Running this script with python2.7 helped me run commands with root privileges.
Yippeee !!! Easy and Good for Beginners :)
Don't forget to study more about SUID ;) Thanks for reading .. !!







Comments
Post a Comment